What is Ransomware, and How Can You Protect Your Company?
Ransomware exploded onto the cybersecurity scene in a big way in 2016, creating a gold rush for cybercriminals. According to recent research, ransomware is now targeting more businesses than consumers and generating huge paydays for the perpetrators.
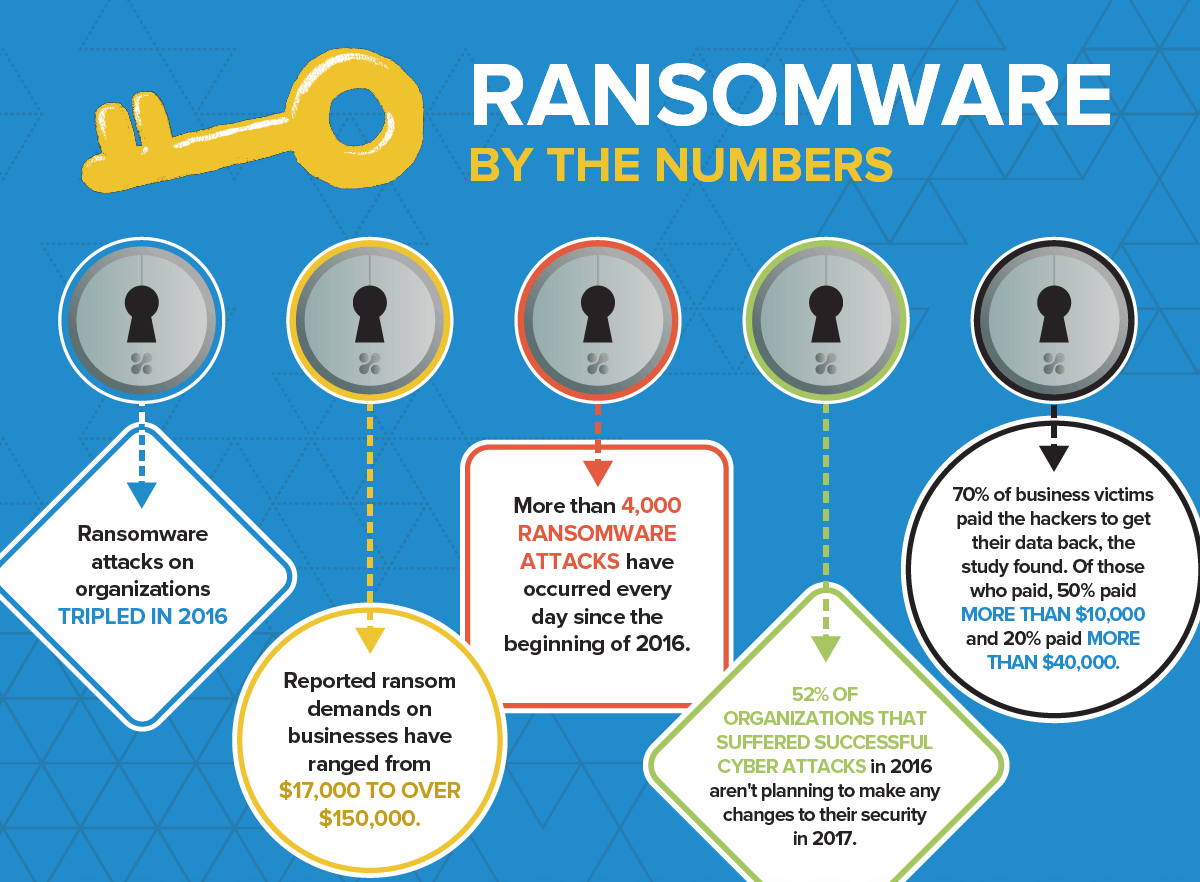
Ransomware By The Numbers
Here are five sobering statistics to keep in mind:
- Ransomware attacks on organizations tripled in 2016.
- Reported ransom demands on businesses have ranged from $17,000 to over $150,000.
- More than 4,000 ransomware attacks have occurred every day since the beginning of 2016.
- 52% of organizations that suffered cyberattacks in 2016 aren’t planning to make any changes to their security in 2017.
- 70% of business victims paid the hackers to get their data back, the study found. Of those who paid, 50% paid more than $10,000, and 20% paid more than $40,000.
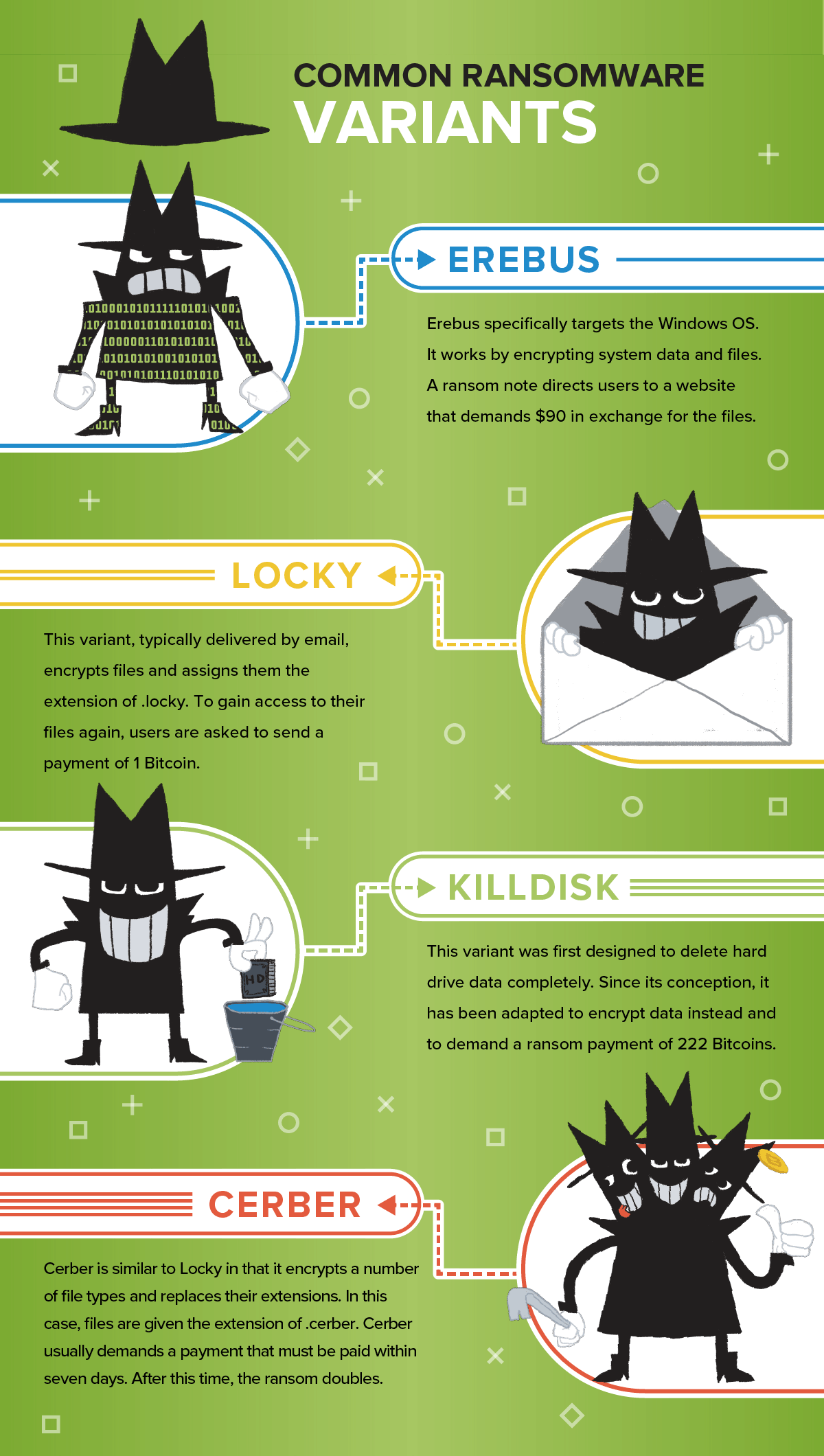
Common Ransomware Variants
These are four common ransomware variants to be aware of:
- Erebus specifically targeted the Windows OS but then resurfaced to target Linux servers. It works by encrypting system data and files. A ransom note directs users to a website that demands $90 in exchange for the files.
- This variant, typically delivered by email, encrypts files and assigns them the extension of locky. To gain access to their files again, users are asked to send a payment of 1 Bitcoin.
- This variant was first designed to delete hard drive data completely. Since its conception, it has been adapted to encrypt data instead and demand a ransom payment of 222 Bitcoins.
- Cerber is similar to Locky in that it encrypts a number of file types and replaces their extensions. In this case, files are given the extension of .cerber. Cerber usually demands a payment that must be paid within seven days. After this time, the ransom doubles.
What To Do Following an Attack
Unplugging machines may be enough to stop the spread to other segments of your network, but you will still need to decide whether you must pay the ransom or not. Backing up your system on a regular basis gives you more options, as you can choose to restore the system to the most recent full backup instead of paying the ransom.
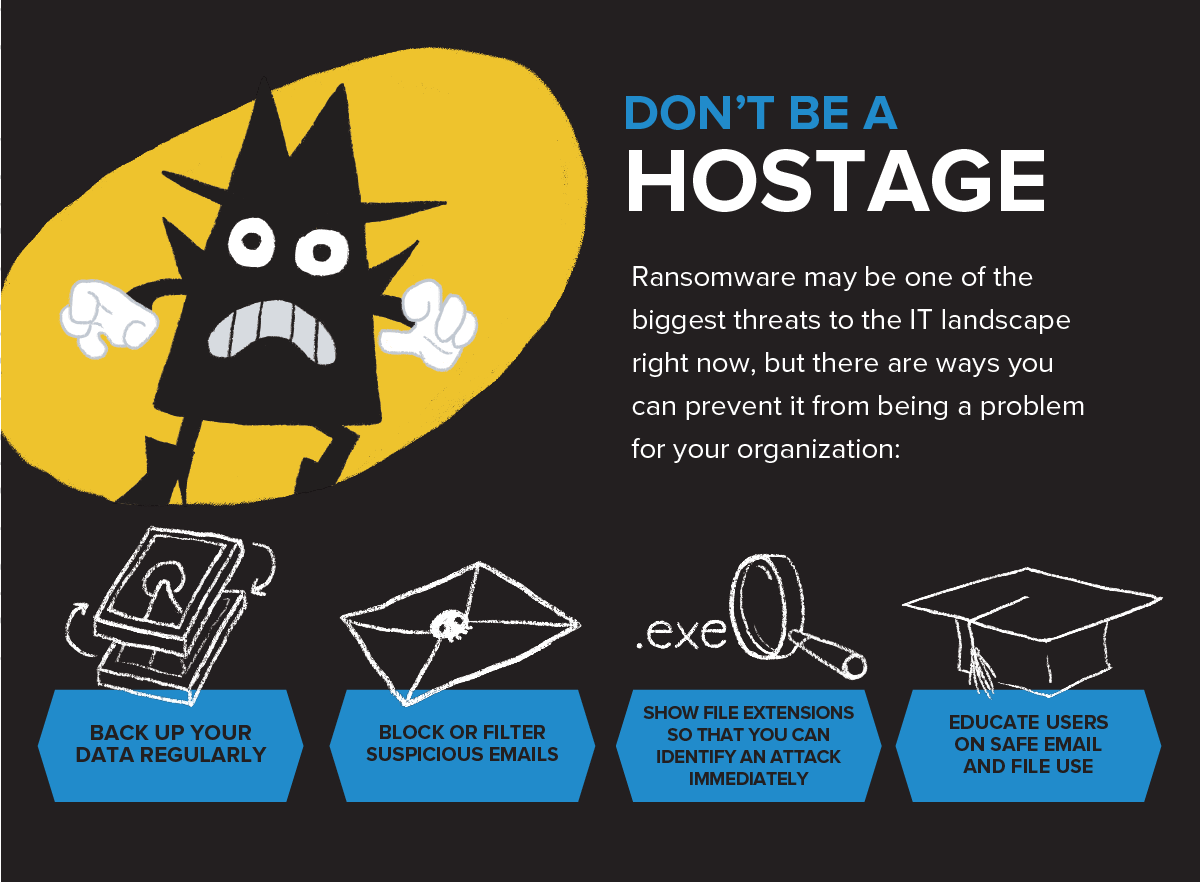
Don’t Be a Hostage
Ransomware may be one of the biggest threats to the IT landscape right now, but there are ways you can prevent it from being a problem for your organization:
- Back up your data regularly
- Block or filter suspicious emails
- Show file extensions so that you can identify an attack immediately
- Educate users on safe email and file use
Conclusion
If you want to ensure that your network is protected against ransomware, DiscoverTec can help. Our IT department can help you set up security measures, educate staff on what to look for, and perform regular backups of your important data. Contact us today if you think you have experienced a systems breach or want to take steps to mitigate the possibility of data loss from ransomware. You can also download our What Is Ransomware Infographic for fast and easy access to the information from this article.