This year, many companies across the world are grappling with the long-term implications of a distributed workforce. Some employers are now fully and permanently remote. Others are bringing team members back to the office, to regain some of the creativity and camaraderie that was lost during the pandemic. Still others have adopted a hybrid model, with remote employees “touching down” at common times and places when in-person collaboration is necessary. In all these cases, remote and hybrid staff need access to sensitive and valuable company data, wherever they are located. Here are the considerations, as well as the steps you can take, to successfully protect valuable data and services with multi-factor authentication (MFA).
Are local network connections really secure?
When employees or contractors are working in-office, data access has an automatic layer of security provided by the local network. One device or system connecting to another on the same network are automatically authenticated because the access connections frequently happen within the same server cluster.
However, when a staff member’s device or system tries to connect from outside the local network, it uses a secured path to send and retrieve data. Two of the most common approaches to provide this access capacity are Remote Desktop Protocol and Virtual Private Network.
Is Remote Desktop Protocol (RDP) or Virtual Private Network (VPN) more secure?
Remote Desktop Protocol (RDP) and Virtual Private Network (VPN) are two of the most popular ways to provide access to remote employees. Each has benefits and drawbacks which are discussed below:
- RDP has a user’s own system behave like a terminal client. Their device uses its internet connection to link up with a server in a data center. When the employee enters their password, they are able to access everything like it was on their own system. However, the user’s profile, applications, email, files, and other resources are all stored on the cloud and do not sit on their individual computer. The employee opens files, edits files and saves files all in the same place: the data center. So, after the password is entered, there is no additional security check or authentication done because all the data the employee is accessing from afar is in the same place.
- VPN allows the users' system to also access the network remotely, but the profile, applications, email, files, and other resources may be stored on their own machine. VPN is a secured tunnel over the internet that allows data to pass back and forth between servers in the data center with the remote client. However, like RDP, there is no additional authentication required while a VPN session is established. So long as the connection is maintained, there is an assumption that every action is coming from the same remote device, because credentials are protected.
The problem with both of these approaches lies in single reliance on the password. When a non-authenticated user gains access to an employee’s password, they can use it to log in through RDP. That non-authenticated user now has access to everything the employee had, but from their own device. That access allows them to do everything the employee could, including taking or distributing valuable information, deleting files or email messages, and potentially other destructive activity. It’s the same story with VPN – they can take whatever the employee had access to and download it to their own machine. But the solution is the same for both approaches: implement MFA.
What’s the difference between 2FA and MFA?
Two-factor authentication (2FA) has been around for decades but historically tied authentication to a USB key or dongle. MFA expanded the authentication into other mediums, such as biometrics, RSA keys, SMS text messages, push notifications, and other secure code schemes. However, 2FA and MFA are essentially the same thing, requiring a combination of two things to authenticate:
- The user’s password
- Something else in the user’s possession
When a remote employee wants to access the company’s data, they log in to their device and try to connect over the internet. After they enter their password, they are prompted by the MFA service to authenticate. Once the employee completes the authentication, they now have access to the data requested. If a non-authenticated user uses that same password, they will not be able to gain the same access, unless they also have access to the MFA service particulars.

What is the best MFA service?
As you might imagine, there are numerous ways to implement multi-factor authentication across your enterprise. There are an equal number of providers whose solutions fall everywhere along the spectrum. Here are a few for quick reference:
- Microsoft 365 is a fully featured application, email, user management and file storage solution that supports single sign-on (SSO) and integrates MFA directly.
- Duo is one of the biggest and most popular MFA services. It integrates to M365 cloud service to make authentication a better overall user experience. And Duo uses SAM/L 2.0 so that it can be integrated with any other supported cloud service.
- Google Authenticate is yet another solution for providing multi-factor authentication but is specially designed to integrate with Google’s ecosystem of applications and storage solutions.
Using one service versus another really boils down to functionality requirements. Each provider varies in functions, pricing, and compatibility. However, as you move forward with a certain approach, it’s crucial to prepare your workforce for the roll-out ahead of time, so that your business can achieve successful adoption and reduce unnecessary service calls.
How to implement MFA across a remote or hybrid workforce using RDP or VPN
Some companies that implement MFA miss an important first step before going live: employee education. Remember that remote access data security is only as good as its weakest link, which is frequently not the system itself. Instead, it is typically user habits that fall outside best practices, specifically with passwords.
Some companies have tried to address this issue by creating policies like requiring passwords to change every three months, or never repeating a password. Unfortunately, these approaches are antiquated and don’t actually address the underlying need: ensuring that employees or contractors who must access data remotely to do their jobs can, without an onerous or overbearing technical process involved. Otherwise, users just create slight variations of the same easy-to-remember passwords (and easy to hack), which aren’t any more secure. So, the goal isn’t to necessarily replace the password. Instead, it’s to put at least two mutually exclusive factors in the right employee’s grasp. The key is that the combination of those actors is difficult or impossible for another user to successfully replicate and gain authentication.
MFA Pre-implementation Tasks
This is especially critical for fintech or healthcare companies, whose data access and security infrastructures are complex, distributed, and provide varying policy levels. We recommend you take these steps before proceeding:
- Establish effective data security policies and review existing ones, making sure they fit the new normal of a remote or hybrid workforce
- Identify all externally facing entry points to your valuable data (examples: VPN, RDP, 365, LastPass, Webmail, etc.)
- Consider the MFA technology (examples: Duo, Microsoft Authenticator, Google Authenticator, etc.) that has the features, pricing, and support you require
- Develop and launch an ongoing, continuous education campaign to help all of your users understand the what/why/how of MFA. This can include form emails.
MFA Implementation Tasks
After the pre-implementation has made progress, it’s time to build out the system. Your IT team should define and document the user experience (UX) for consistent adoption. They will likely be very involved in the ongoing user education portion of the initiative, helping populate training materials with screenshots and other content to help employees better understand how to follow the new process. At the same time, your IT team will manage the installation and configure everything to properly function as intended, performing UAT and PIV. Also, your development team might need to be involved to protect custom applications.
Additional Tips to Best Leverage MFA For Optimal Data Security
Even with a compelling, mandatory, and participatory employee training regime, plus a buttoned-up MFA system configured by the team perfectly, problems still happen. Unfortunately, there is no way to completely engineer around the human condition by seeking paths of the least resistance. The same things that make MFA authentication easy may be the same places for system failure.
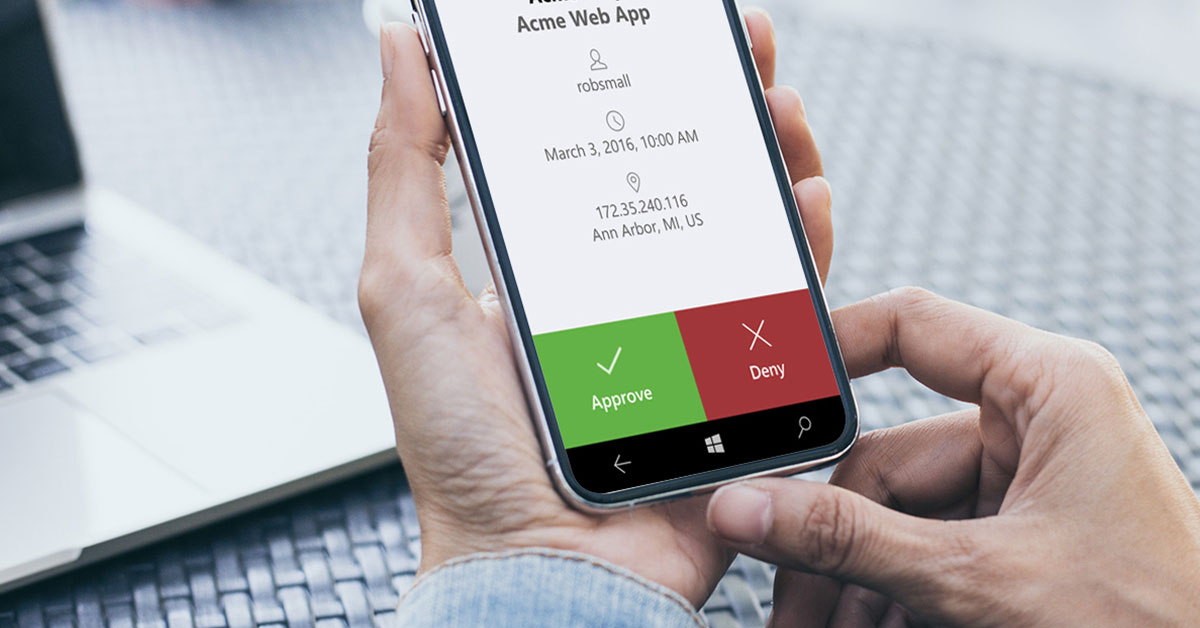
- Push notifications. Think about how often you experience desktop or mobile device notifications during the workday. Once an hour, twice an hour, or even one every 10-15 minutes?
Many employees have developed “notification fatigue” where they automatically click approve on pop-ups, just to continue working on what they are working on. Therefore, push notifications can present an easy social engineering opportunity for external groups to gain unauthorized access, then exploit your network and data. Coming full circle, education is important… but employees must take a moment to pause, read, consider, and judge the veracity of a notification.
- Least privilege access. Think about the local admin policy for remote employees, then consider what files or applications they need remote access to, and which can reside on their local system.
There is a significant cost in service calls that come in for basic configuration adjustments. Instead of an IT team addressing external security threats or system downtime challenges, they may be bogged down, dealing with application installations. Consider how to white list certain application installations from a network resource, so that you provide an adequate self-service solution to staff while maintaining version control and overall access safety.
- User ease and delight. As much as possible, put yourself in the shoes of the user. How can system policies and authentication tools be best implemented to avoid potentially disastrous workarounds?
We want to harness the creativity of your workforce to solve business problems, not struggle with authentication regimes. With careful consideration of the user experience around security and authentication, you will gain enthusiastic advocates, instead of begrudged policy-followers. Put the users’ needs first, and build out the methodology, process, and education around those priorities. By doing this, you will find that implementing multi-factor authentication effectively secures all of the valuable data and systems that your enterprise relies upon.